WordPress has become the most popular CMS (Content Management System) in the world. It is used to power about 75 million websites, which equates to more than 27% of all websites on the Internet using a content management system.
Unfortunately, because WordPress is so popular, it is a prime target for malicious hackers. WordPress security company Wordfence estimates that there are currently between 25 to 45 million brute force attacks on websites running WordPress each day — a scary figure! Hackers also target the WordPress codebase, WordPress themes, and WordPress plugins.
To protect your website from these attacks, it is important to regularly update your WordPress installation and ensure your web server is secure. We recommend Siteground. You can also use a WordPress security plugin to ensure various aspects of your WordPress installation are secure.
One of the best tools for securing a WordPress installation is the iThemes Security Plugin. It is a powerful security plugin that is simple to use and greatly reduces your risk being hacked by malicious entities. This guide will explain some of the security threats common to WordPress and how to setup iThemes Security Plugin.
Table of Contents
- Why do hackers target WordPress sites?
- How is WordPress most commonly attacked?
- Installing iThemes Security plugin
- Getting started with iThemes Security Plugin
Why do hackers target WordPress sites?
Hackers attempt to gain control of WordPress sites for a number of reasons, including:
- To steal your website’s data: Hackers may be interested in obtaining your private data or the data of your customers. They may sell that data or send spam to the email addresses they harvest.
- To host malicious content: Hackers often place malicious content on the websites they have hacked. This could include spyware, deceptive web pages or other forms of malware.
- To attack other websites: Hackers can use vulnerabilities in your website to make it a tool for attacking other websites.
- To send spam: Some hackers look for WordPress sites with vulnerabilities that help them to send spam. Because the spam will be sent from your WordPress installation, it may cause your website to become blocked by spam filters.
How is WordPress most commonly attacked
WordPress is one of the most secure content management systems available. However, there are still security vulnerabilities that appear in the core code of WordPress, the plugins and certain WordPress themes.
A paper published by https://wpscan.org/ suggests that there are almost 4,000 known WordPress security vulnerabilities across all versions of the application. 52% of exploits are caused by issues in WordPress plugins, 37% are relating to exploits in the core code of WordPress, and 11% are caused by issues with WordPress themes.
The most common techniques used by hackers to obtain administrator-level access to a WordPress installation include:
- Brute force attacks: This is perhaps the simplest attack on a WordPress installation. The hacker tries many different usernames and password combinations in an attempt to access the installation’s control panel. WordPress does not come with brute force attack protection, but you server provider may use software to prevent this kind of attack.
- SQL Injections: Hackers use web forms to send raw SQL to your database. If their attacks are not handled appropriately, they may be able to add, remove, or modify sensitive information in your database.
- File inclusion exploits: WordPress themes and plugins often include additional files that add functionality to the core application. Hackers often attempt to have their own files included in an attempt to compromise the installation.
- Malware: Malware is malicious software that can be used to compromise a software installation. There are many types of malware including malicious redirects, computer viruses, worms, and trojan viruses. It is important to scan your WordPress installation and ensure no malware is present.
Installing the iThemes Security Plugin
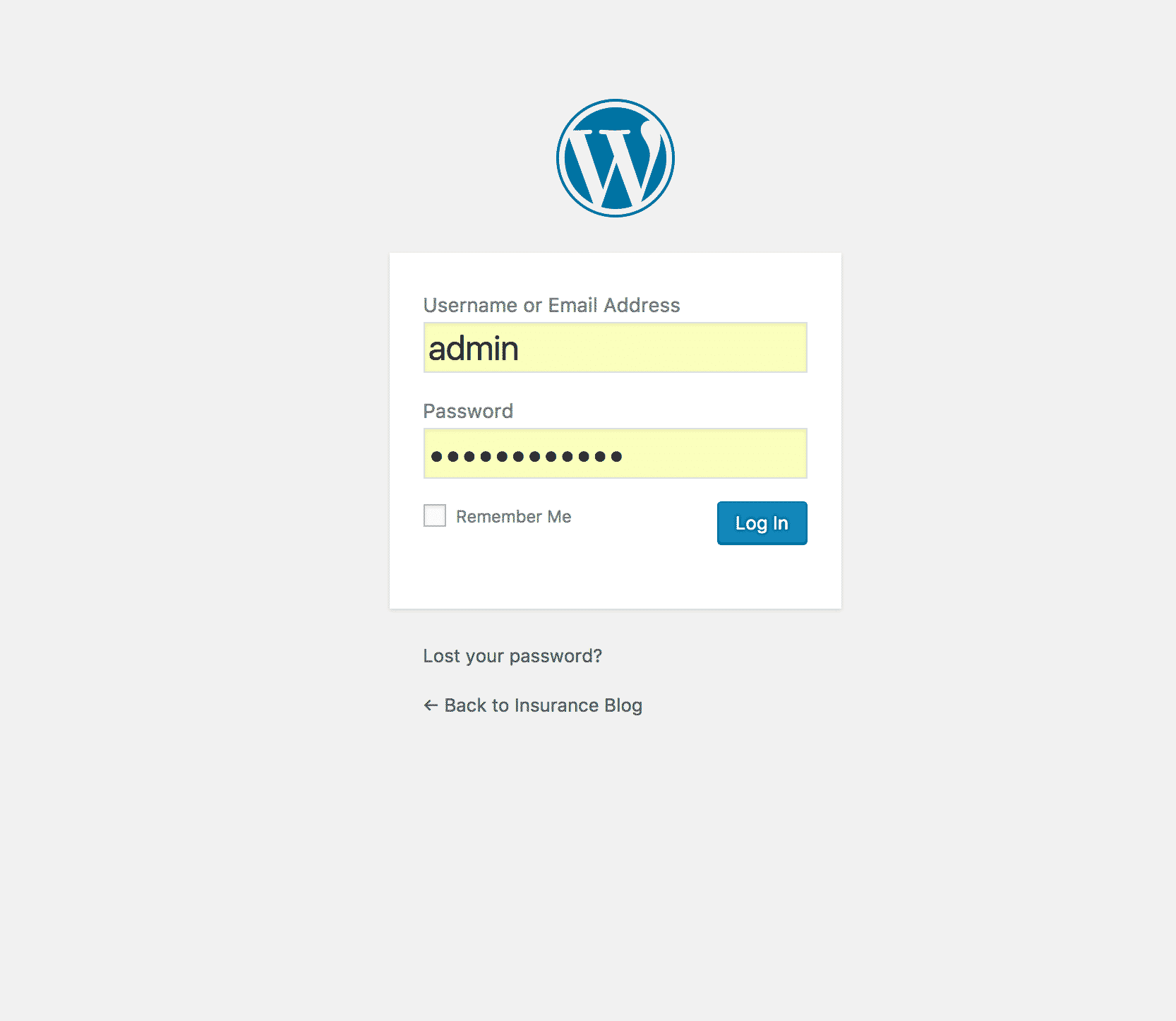
The installation process for iThemes Security Plugin is very simple. However, before you begin — backup your WordPress installation. The iThemes Security Plugin is very powerful and can make significant changes to your site. Have a backup ready in case you accidentally tweak the wrong setting. The installation process is as follows:
1. Log into the administration section of WordPress
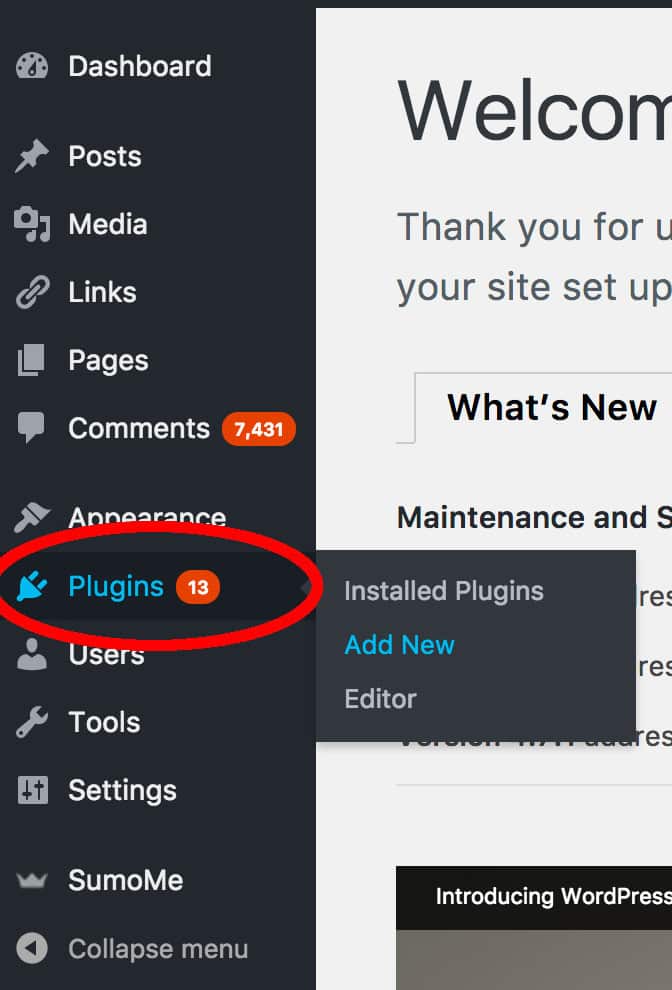
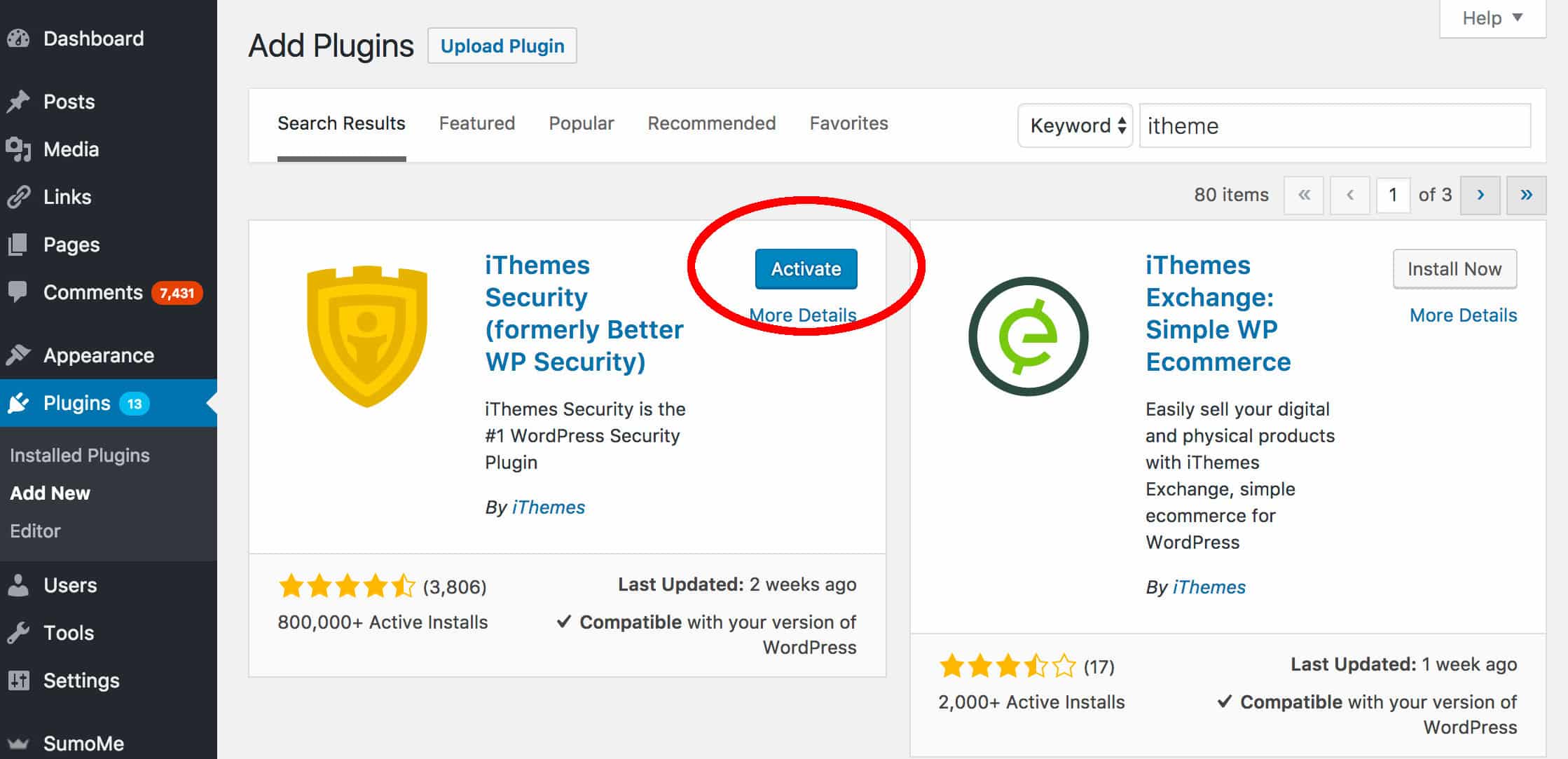
2. Hover over the “Plugins” menu item on the left-hand side and click “Add new”
3. Search for the iThemes Plugin by typing “iTheme” in the right-hand search box. In a couple of seconds, the search results will appear. When they do, click “Install Now”.
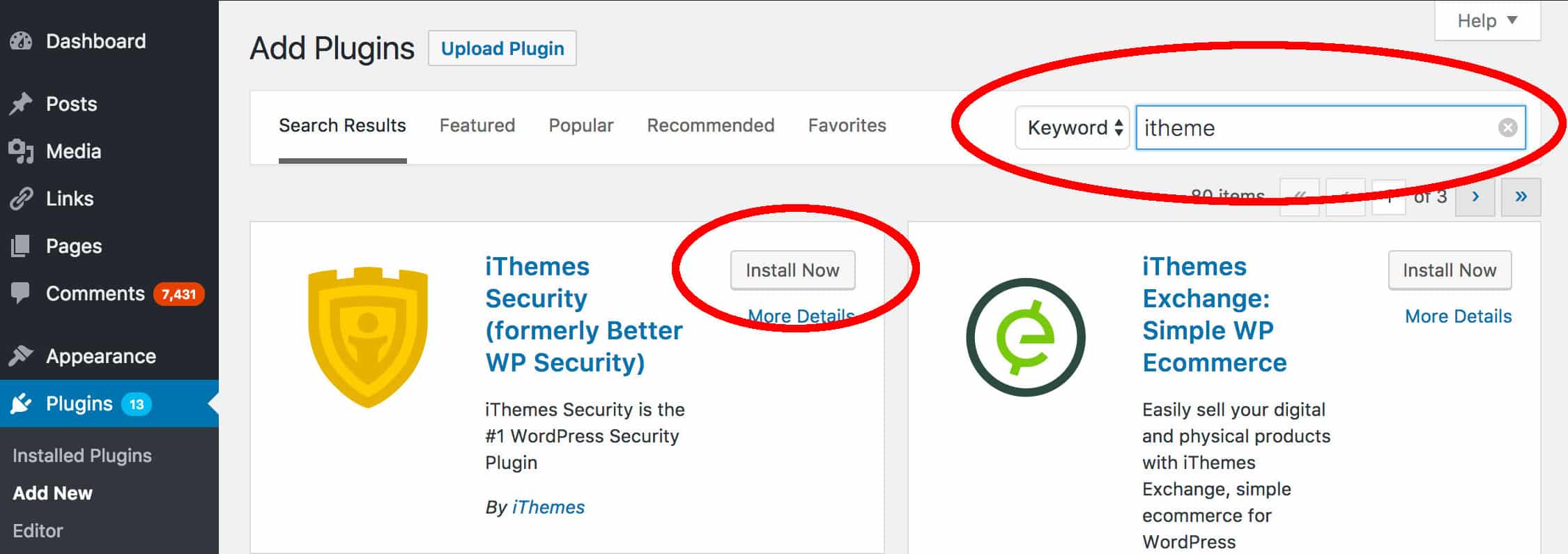
4. Activate your plugin by clicking “Activate”. You are now ready to roll!
Getting started with the iThemes Security Plugin
Once the plugin has been installed, you will see a new menu item on the left-hand side titled “Security”. Click on that menu item to view the four menu items:
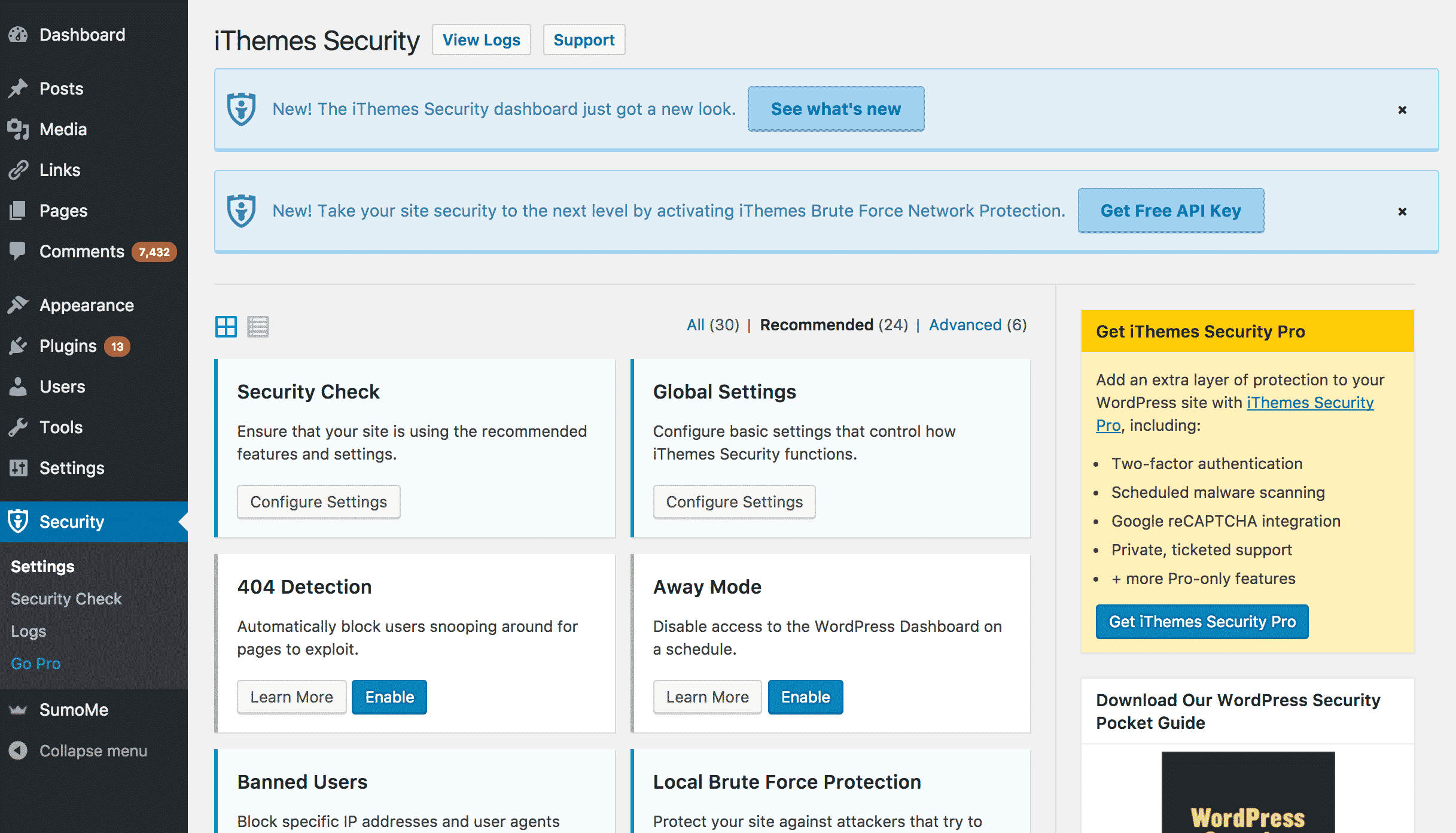
- Settings: Where you can modify the plugin’s basic settings and turn modules on or off.
- Security check: A quick start process where the plugin takes a look at the current security of your WordPress installation and enables some essential modules.
- Logs: The plugin keeps logs for invalid login attempts and malware scans. Those logs are displayed here.
- Go Pro: Users can upgrade to the pro version of the plugin, which includes more functionality.
The plugin uses security “modules” that deal with security issues that often affect WordPress installations. You can enable the modules you think your website requires or run a “Security Check”, which enables the most useful security features that the plugin has to offer.
To begin, click on the “Security Check” menu item on the left-hand side. You will see a message that describes which modules will be enabled during the process.
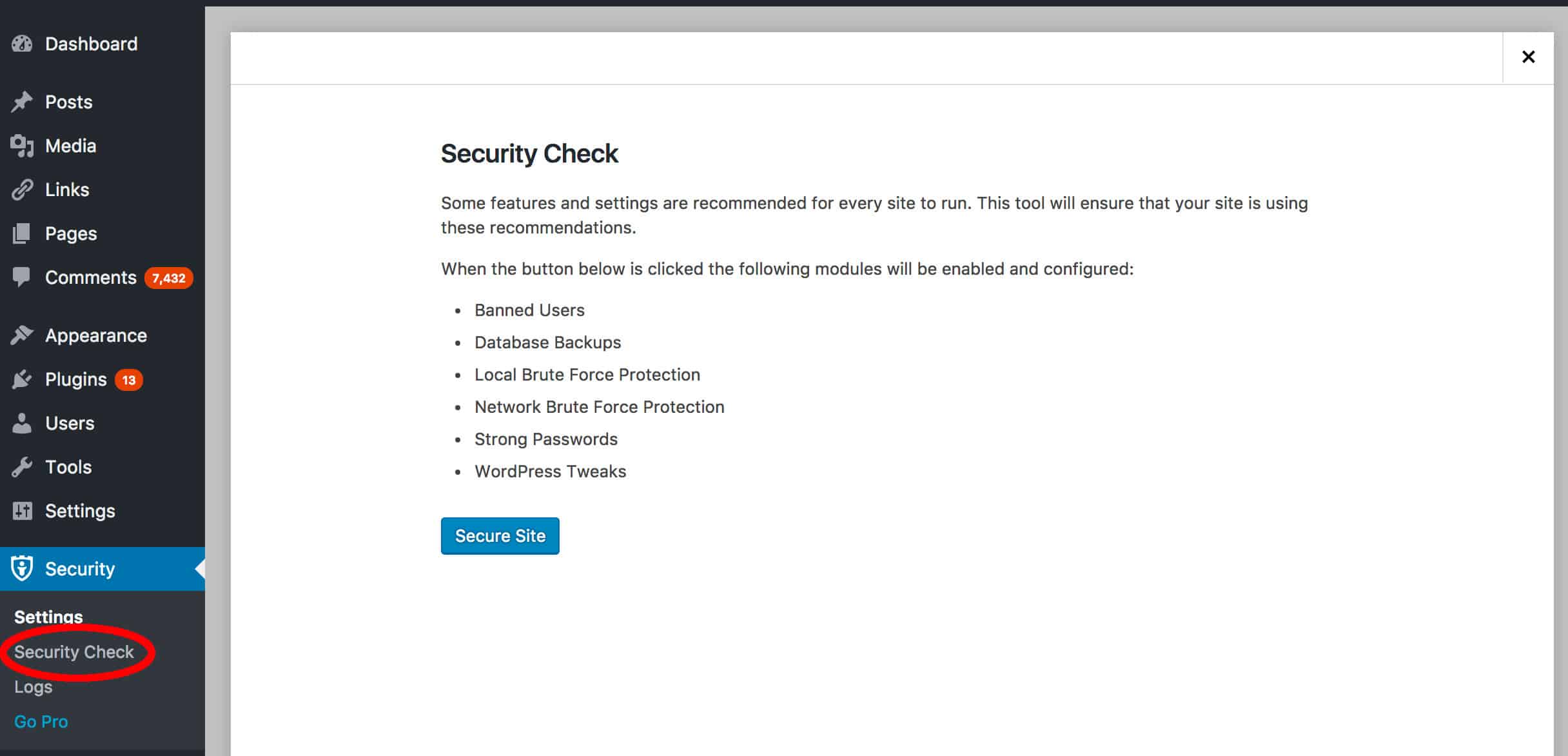
Click “Secure Site” to get started.
You can now configure the modules that have been activated. Press the close button on the Security Check popup to get started. You will be at the “Settings” screen and be viewing a list of the available modules.
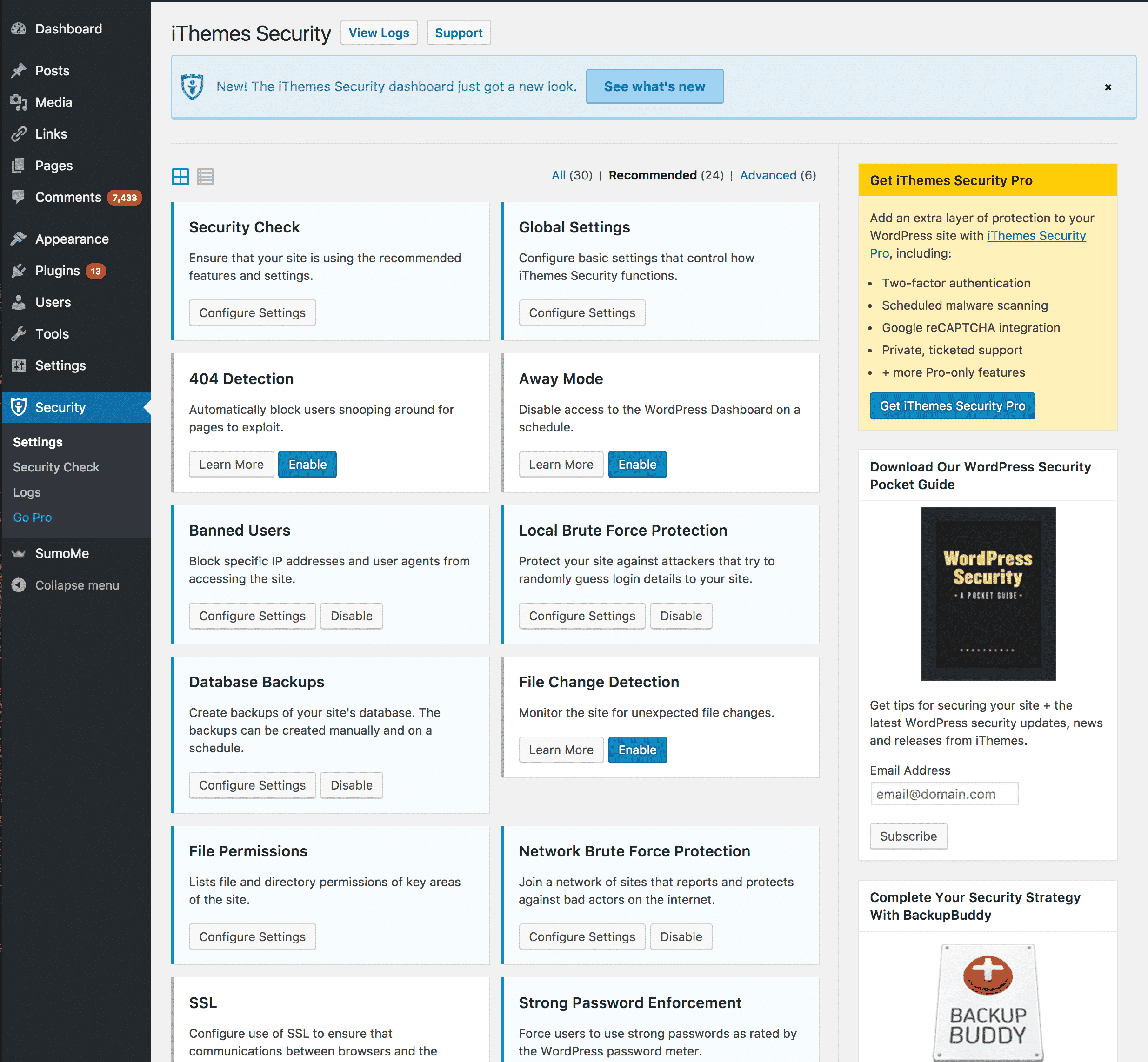
The following modules will be activated, so we’ll go through them and make the necessary changes to settings.
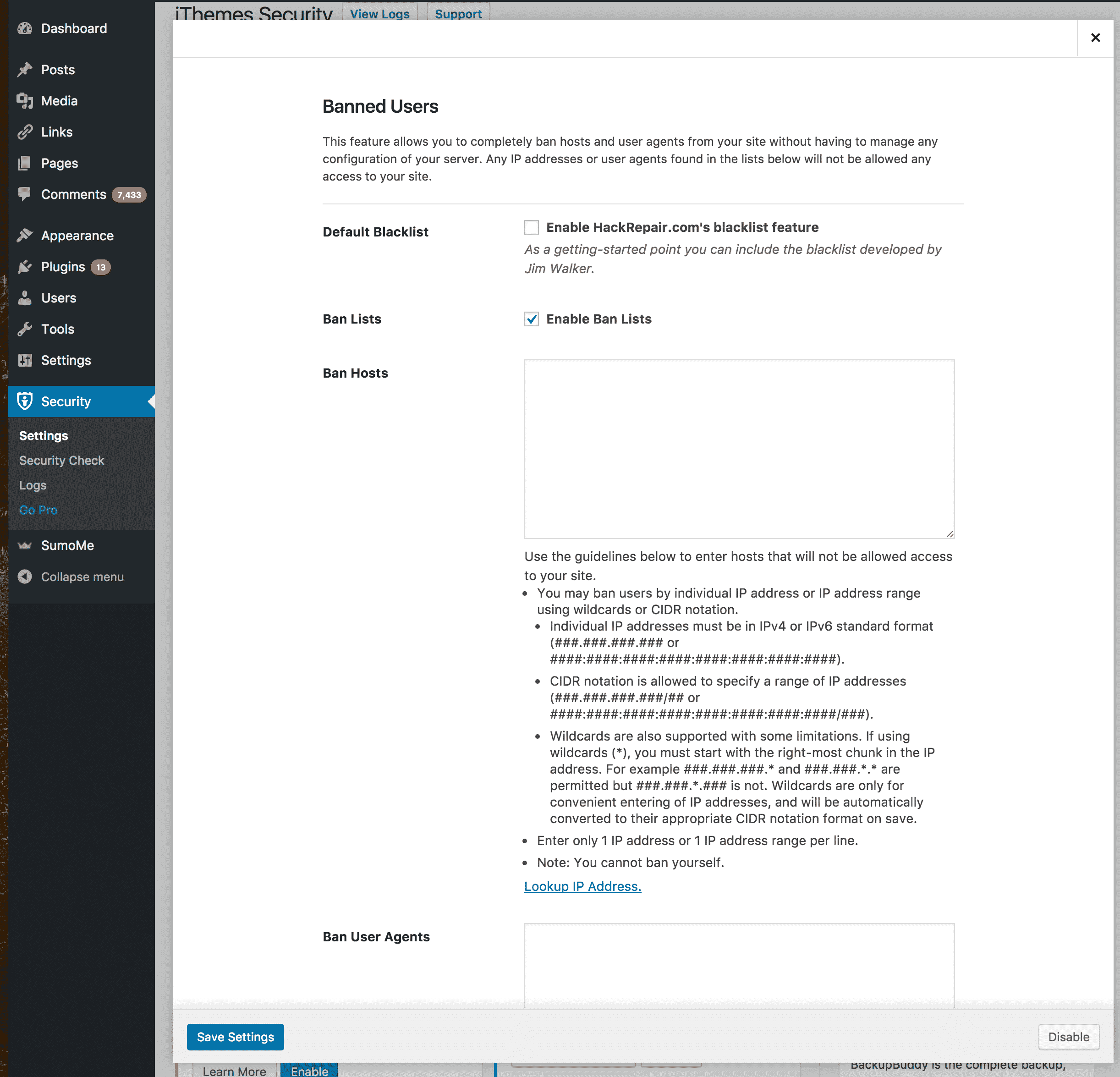
1 – Banned users module
This module allows you to ban internet protocol addresses and user agents from your website. If you notice that certain users or web hosts have been using the website inappropriately, you can enter their IP address in the configuration section of the module. This will ban them from your website. You can also enable the HackRepair.com blacklist, which is a large list of IPs identified as behaving maliciously.
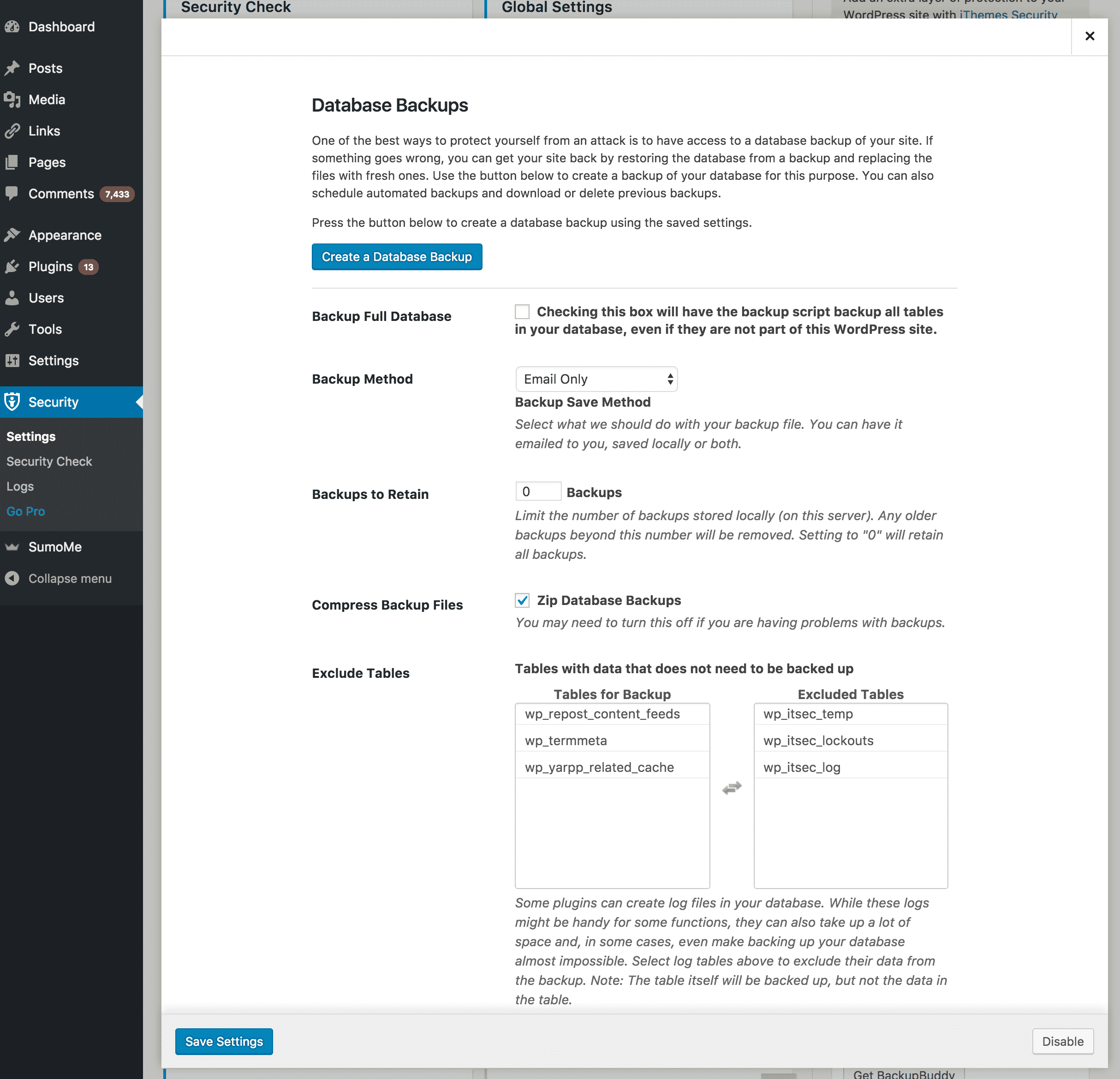
2 – Database backups module
Having database backups is an important part of securing your website. Think of it as an insurance plan for your website — you will be able to quickly restore your website after a malicious attack has occurred. This module will automate the backup process for you.
It has many different options including where to store the backups, how many backups to keep, which database tables to exclude from backups and when to schedule backups. Alter these settings as you see fit.
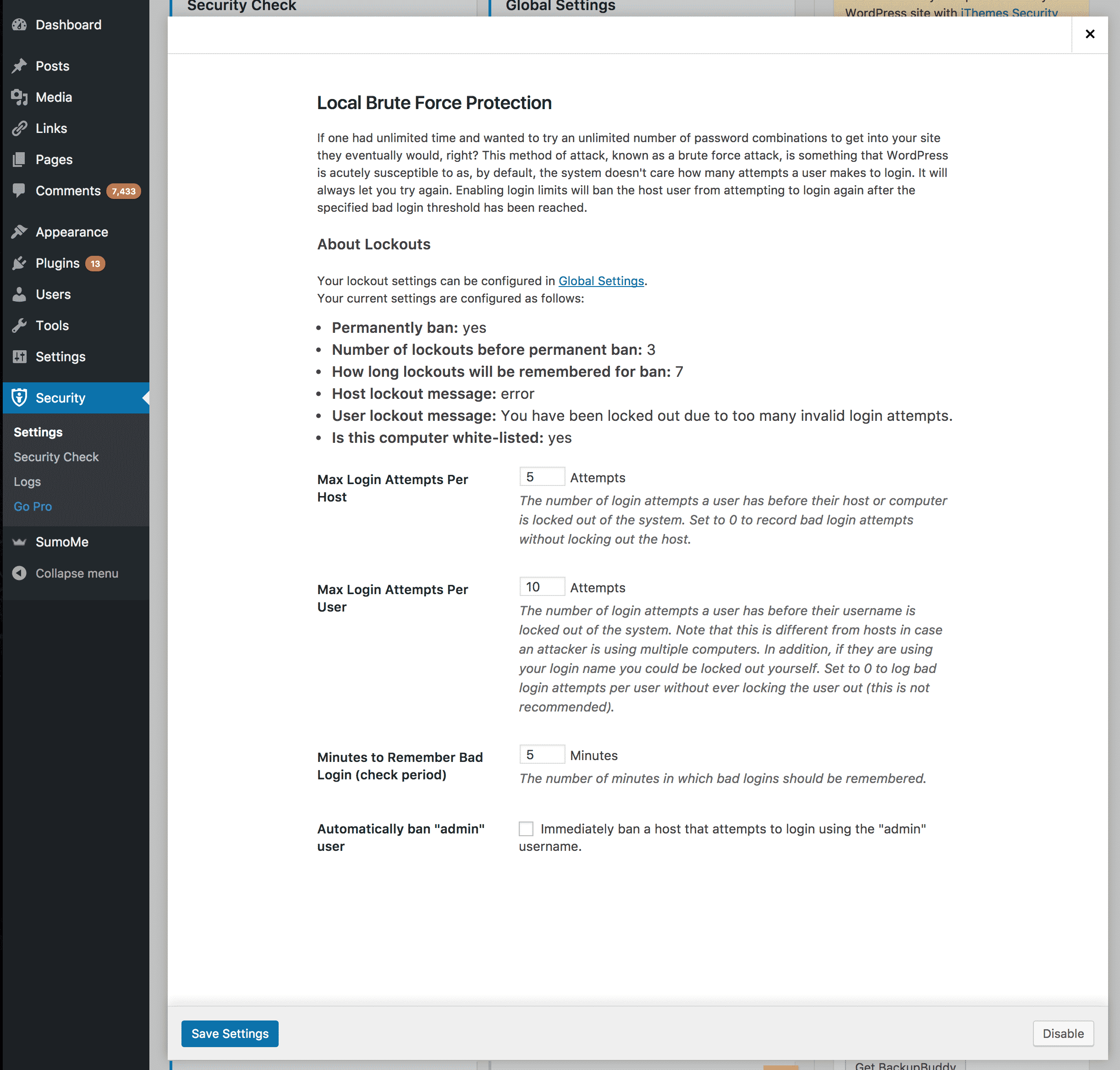
3 – Local brute force protection module
This module prevents users from repeatedly attempting to log in to your website (a brute force attack). You can alter how many log-in attempts are allowed for a user before they are banned, how long they are banned for and much more. This will prevent malicious entities from eventually guessing your username/password and gaining access to your website’s administration section.
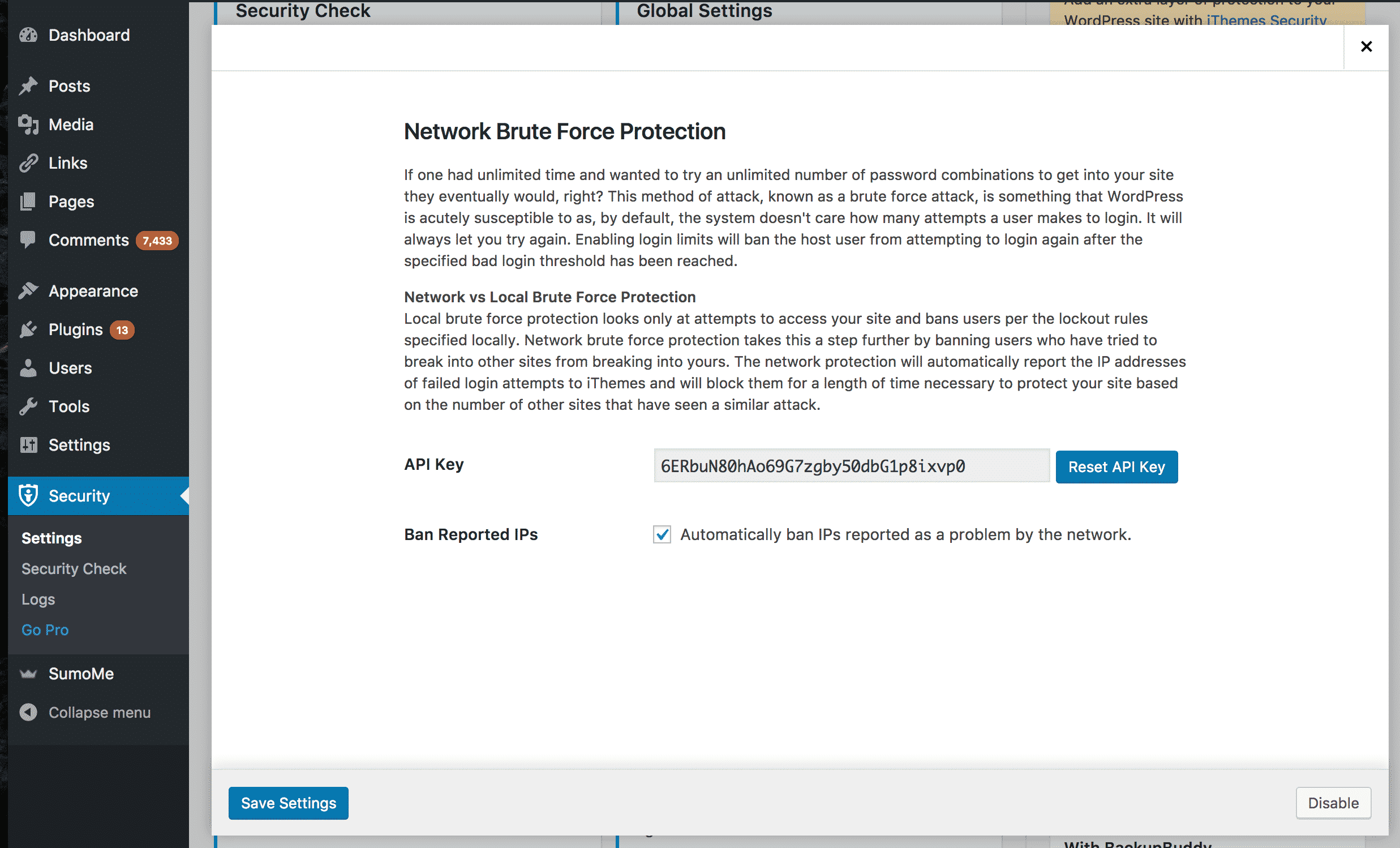
4 – Network brute force protection
The Security Check feature also enables the Network Brute Force Detection module. In addition to banning users who have attempted a brute force attack on your website, this module can ban users who have attempted brute force attacks on other people’s WordPress installations.
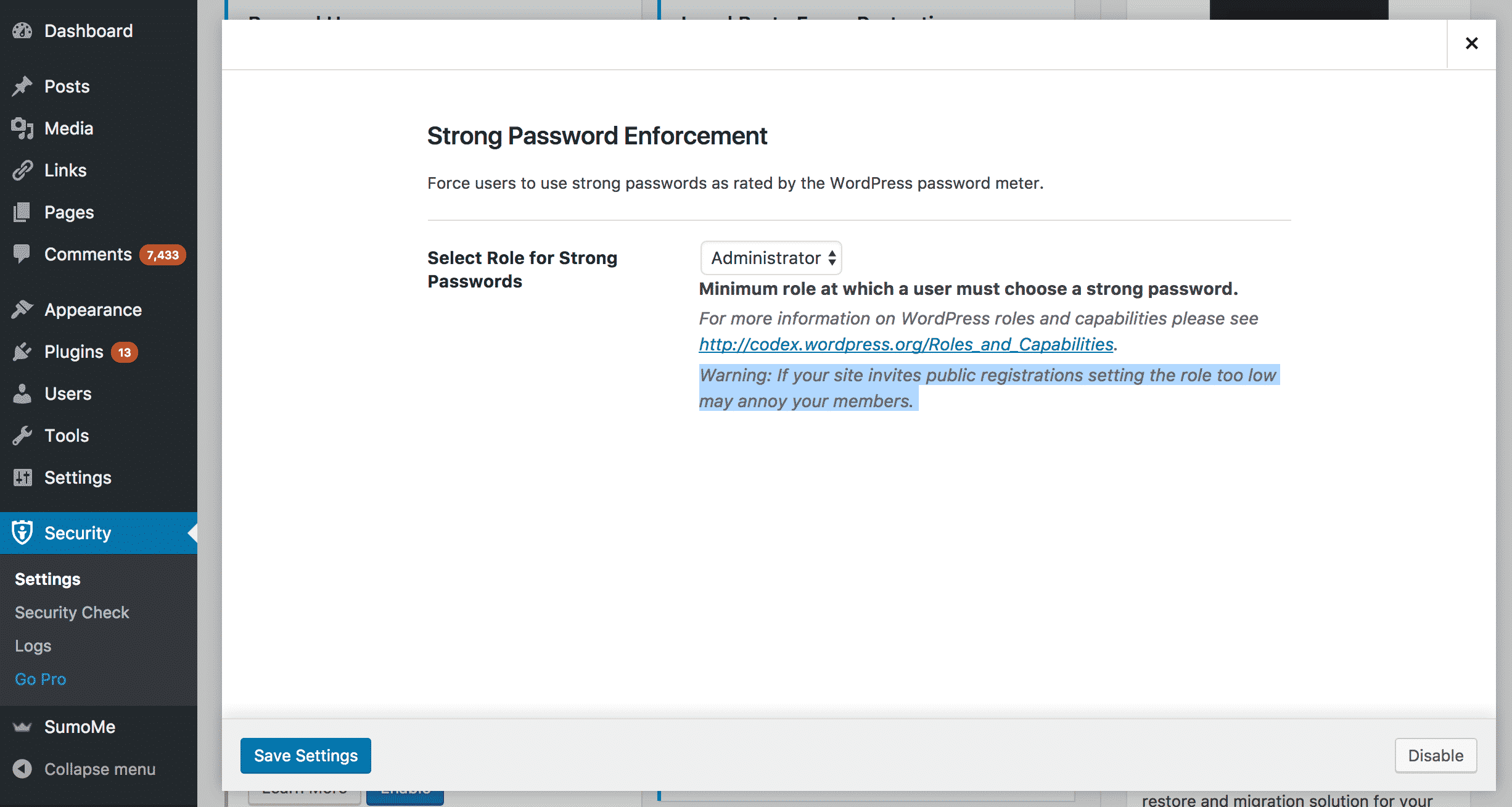
5 – Strong password enforcement module
This module makes WordPress demand more secure passwords from users who join the site. You can set which types of users are forced to have a strong password. Pretty handy when running a multi-author website.
6 – WordPress tweaks module
This module contains many optional changes that can make your WordPress installation safer. These options include:
- Disabling the WordPress file editor (a target for exploits)
- Disabling XML-RPC access (a target for exploits)
- Removing the Really Simple Discover header from code (which can make it hard for hackers to find your blog)
- Automatically reduce comment spam
- Replace jQuery with a safe version (reduce the risk of a Javascript exploit)
Enable or disable tweaks to suit the requirements of your blog.
Configure global settings
The next step it to alter your installations global security settings. You will find the global settings module near the top of the “Settings” page.
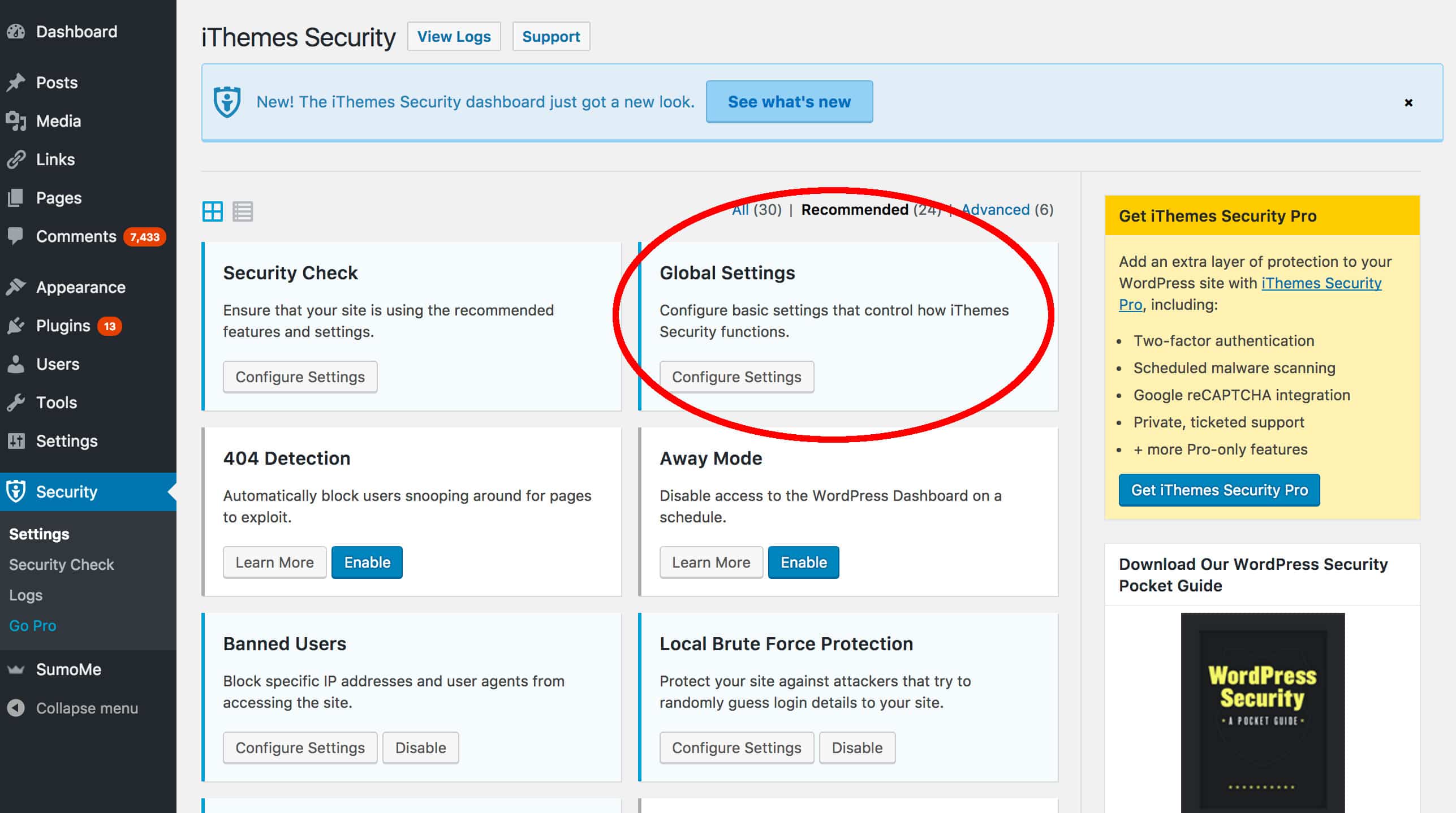
There are dozens of settings here, which you can configure to suit your requirements. The most important settings include:
- Notification email — where to send emails with details of security events
- User lockout message — what to show users who have been banned
- Blacklist settings — the Blacklist repeat offender, blacklist threshold, blacklist lookback period, and lockout period will determine how you handle offenders
- Log type — determine how much information you retain on security events
Enable other modules
Now that you have the most important modules configured, you can explore the other options that iThemes Security Plugin has to offer. Go to the settings page once more and toggle the “module view button” to display all modules as a list. This will make it easier to view the remainder of the modules.
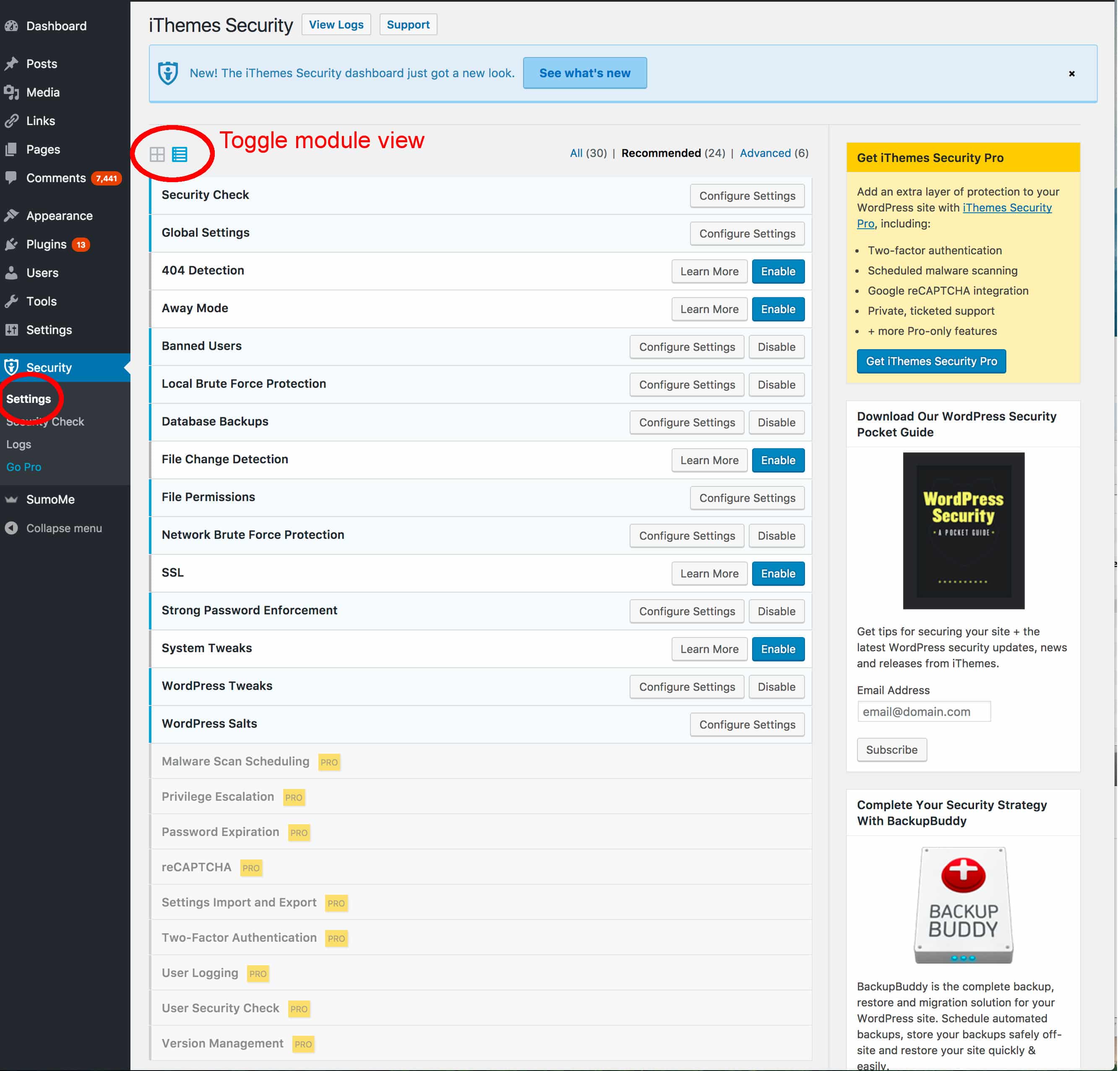
The remaining modules include:
- 404 detection module: This module identifies users who are hitting many non-existent pages. Hackers sometimes do this when they are looking for an entry point into the administration section or a page with some kind of vulnerability.
- Away mode module: Most website owners only update their site during certain times of the day. This feature allows you to disable access to the WordPress administration section at other times. This will prevent hackers attempting to break into your site at 2 in the morning!
- File change detection module: Hackers who gain unfettered access to a WordPress site often make small changes to the site’s code. This module will look at the files to determine if anything has been changed.
- File permissions module: It is easier to hack a website that has file permissions that are too lax. This module will check the file permissions of your WordPress installation and suggest fixes.
- SSL module: Secure Socket Layers (SSL) encrypts the data that is sent between your website and a visitor. This module will turn SSL on for your WordPress installation if your server supports it.
- System tweaks module: These are advanced settings that can improve the security of your installation. They mostly deal with directory, file and PHP security.
- WordPress salts module: A salt is a random string that is used when creating passwords. This module will help you quickly update your WordPress salt.
Consider Going Pro!
The professional version adds even more functionality to iThemes Security plugin. Some of these features are very useful, particularly if you are running a business website on WordPress and require a high level of security. The Pro features include:
- Malware scanning: The plugin will scan your WordPress directory for malware
- WordPress two-factor login: Makes users enter a password and a secondary code that is sent to their mobile device before logging in. This is an excellent way to secure your administration section.
- WordPress user security check: Allows you to view the logged in status, password safety level, and two-factor authentication status of all users.
- reCaptcha integration: reCaptcha is a system designed to ensure only real human users can access content or log in. The pro version of iThemes Security Plugin allows you to easily integrate reCaptcha with your WordPress installation.
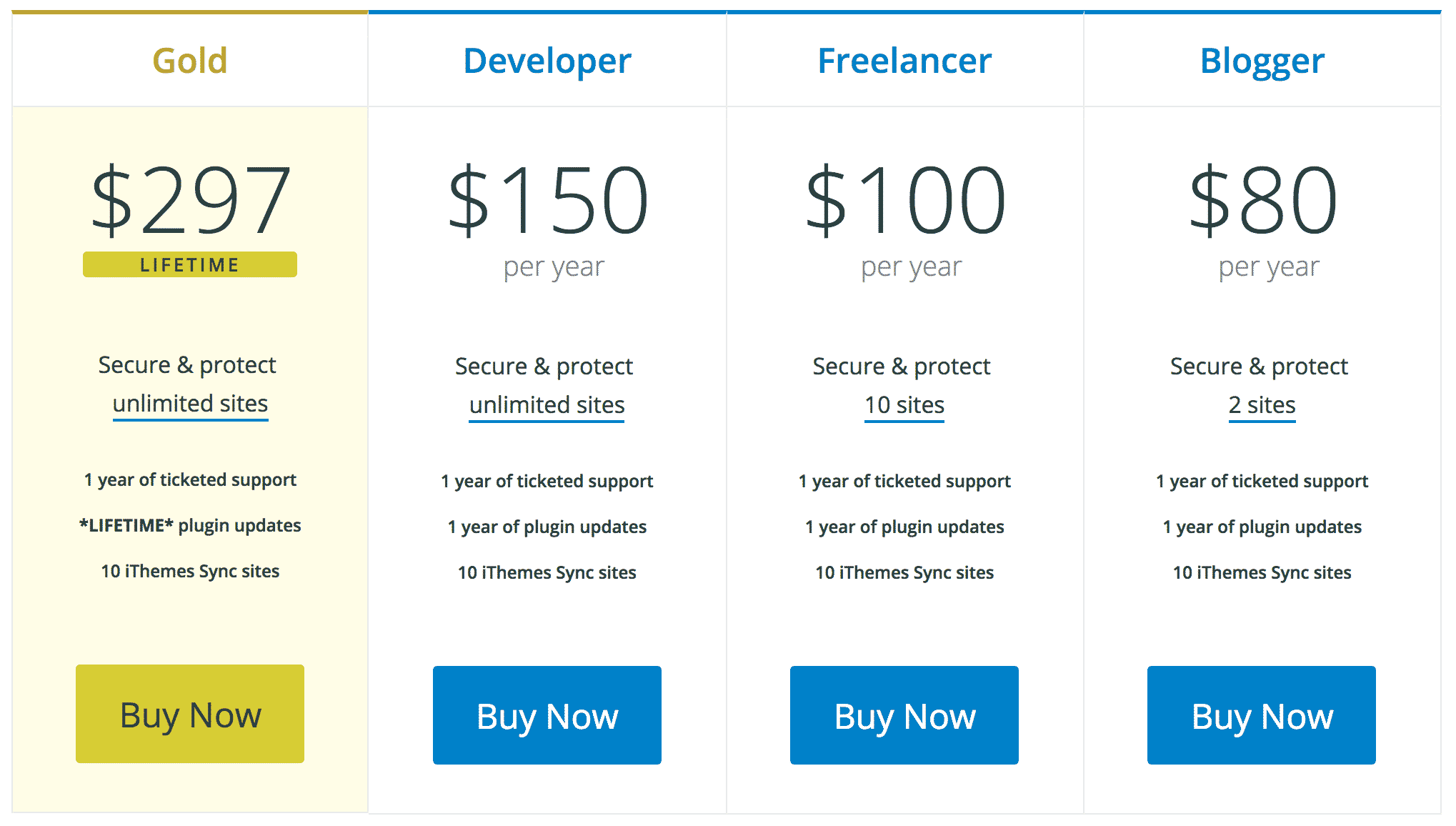
The pricing for the pro version of iThemes is quite reasonable and at the following levels (April 2017):
We hope you enjoyed reading our complete step-by-step guide to the iThemes Security Plugin! It is a fantastic addition to any WordPress site and one of the strongest security plugins available.